By Nils Solvang, Managing Partner.
 This series of posts look at some of the complexities of Cyber Security. Why do many organisations struggle with the softer side of this conundrum?
This series of posts look at some of the complexities of Cyber Security. Why do many organisations struggle with the softer side of this conundrum?
The first post <find it here> considered some key characteristics of a good Chief Information Security Officer (CISO). In this second post, we look at the organisation and culture that surrounds the CISO.
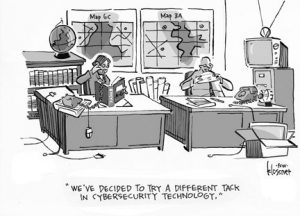
Where should a CISO sit in an organisation? The position needs influence, independence and a trackable budget. To find the right model it is important to consider the CISO’s strengths. Many come from a strong technical background and may favour expensive and complex technology safeguards to mitigate security risk.
Technology is important, but it is vital that such solutions are independently verified in terms of real business benefits. Work out the expected business benefits based on realistic costing. If the ongoing cost of a safeguard exceeds the estimated loss expected from a breach, it is obviously better to do nothing. Although the CISO holds the budget, ensure that independent Technical and PMO resources verify the business benefits of a Cyber Security project.
On the other hand, if someone else like a Chief Information Officer (CIO) fully controls the Cyber Security budget, the temptation will be to overly favour other objectives, typically being operational savings or quicker product development. In other words, the best organisational position for a good, balanced CISO is as high as possible with as much independence from C-grades with conflicting objectives as possible, but ensure verification and organisational adjustment given the CISO’s background and strengths.
Should the CISO run an independent Cyber Security organisation? There is one truism in Cyber Security: If staff do not understand the reasons behind protective measures, they are going to circumvent any security implements that inconvenience them. This again comes back to the CISO’s preferred prime characteristic as a great communicator and leader in order to educate staff as to why the initiatives are implemented.
Consequently, a large, dedicated security organisation reporting to the CISO may actually be working against developing a pervasive security consciousness as staff feel that Cyber Security is ‘not my problem’. Additionally, the CISO gets bogged down in people management, taking up valuable time. A virtual or matrix model where IT and Network staff in particular are actively involved in planning and implementing security into services, infrastructure and processes can often be a better, more inclusive model.
Regardless of the organisational structure, the CISO needs access to resources to help communicate, train and upskill staff to develop an understanding and culture of following good Cyber Security practises.
For informal discussion on Cloud Migration in particular contact CloudCIO
Look out for the next post tackling Technology and Infrastructure.
